Black Hat Python: Python Programming for Hackers and Pentesters: Seitz, Justin: 0884841511358: Amazon.com: Books

Types Of Hackers: Black Hat vs White Hat vs Grey Hat | Cyber Security | #Shorts | Simplilearn - YouTube

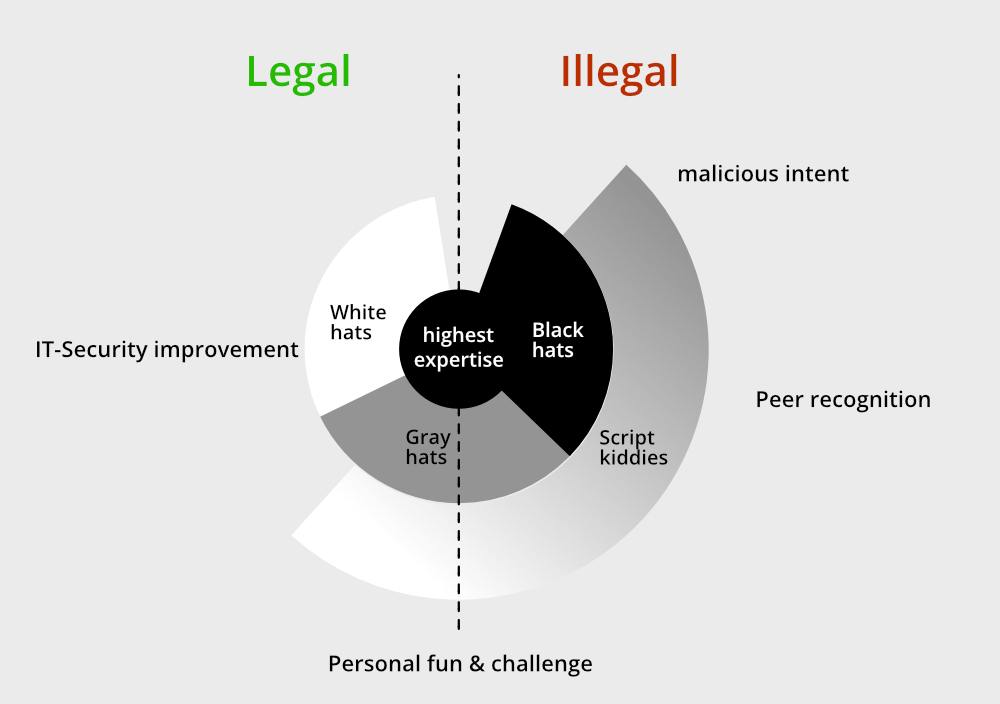
Ethical Hacking White Hat Hacker Vs Black Hat Hacker Ppt Example File | Presentation Graphics | Presentation PowerPoint Example | Slide Templates

Buy Certified Blackhat: Methodology to Unethical Hacking Book Online at Low Prices in India | Certified Blackhat: Methodology to Unethical Hacking Reviews & Ratings - Amazon.in

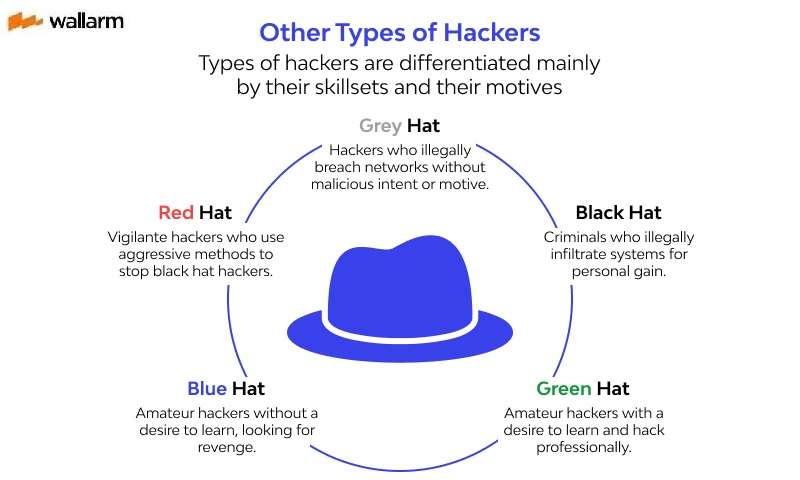
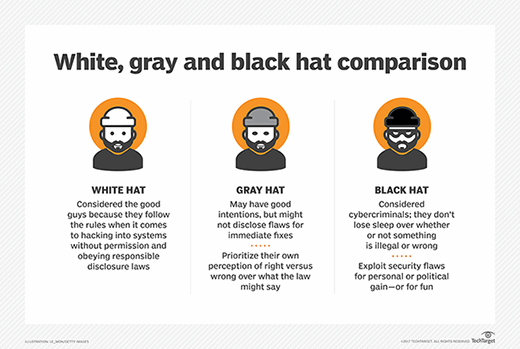
7 types of computer hackers - White hat, Gray hat, Black hat, Green hat, Blue hat, Red hat - YouTube






![What is Ethical Hacking? A Comprehensive Guide [Updated] What is Ethical Hacking? A Comprehensive Guide [Updated]](https://www.simplilearn.com/ice9/free_resources_article_thumb/ethical_hacking_infographic.jpg)